Unattended devices are making waves across multiple sectors, ranging from retail and transportation to healthcare. And it’s easy to see why. These gadgets bring efficiency and self-reliance to everyday operations and tasks, even when human supervision is limited.
However, the true potential of these devices shines when you pair them with unattended remote desktop solutions like RemoteToPC. Using the software, you can remotely manage unattended devices and boost business productivity.
In other words, this can be your game-changing combination to streamline business operations, improve security, and make technology accessible like never before.
Ready to discover the why and how? Keep reading!
What Are Unattended Devices?
Unattended devices are pieces of hardware designed to operate independently, i.e., without the need for constant human supervision. Their design allows them to function autonomously and serve a variety of purposes depending on the industry.
A few popular examples of these devices include self-checkout counters in retail stores, ticket vending machines in transport terminals, and informational kiosks in healthcare settings.
It’s also worth noting that unattended support is generally built into these devices, allowing them to execute every task efficiently.
What is Remote Management?
When discussing unattended devices, it’s essential to grasp the concept of remote management. It’s the practice of controlling and administering hardware and software systems from a distance using secure remote access technologies.
Simply, it allows you unattended remote access to perform tasks that typically require physical presence, such as software installation, updates, and troubleshooting.
The key tool often employed in this practice is remote desktop assistance. This boosts the capabilities of unattended gadgets and makes it possible to control an entire fleet of devices seamlessly, irrespective of their location.
Why Combine Unattended Devices with Remote Management?
While unattended devices can be incredibly beneficial, they aren’t without challenges. Issues like power outages, network glitches, or system hiccups can disrupt services and frustrate customers (and even remote employees). That’s where the collaboration of remote desktop assistance and unattended gadgets comes in handy. It offers the following benefits:
1) Streamlining Operations
Imagine not having to visit each unattended device individually for maintenance or updates. That’s the beauty of integrating remote management into your operations. It allows your tech team to perform essential tasks—like software updates and troubleshooting—on multiple devices across various locations, all from a centralized hub.
This unattended remote access feature will save valuable time and resources, making your business run more smoothly and efficiently.
2) Enhancing Security
Did you know that more than 84% of organizations employ IoT devices? Yet fewer than half have implemented strong defenses against cyber threats. This is indeed shocking information, considering unattended devices are often vulnerable to security threats. To prevent such a situation, it’s recommended to use robust remote access solutions like RemoteToPC, equipped with EV-SSL and 256-Bit + Poly-1305 AEAD P2P encrypted tunneling. It’ll ensure that the transferred data is well-protected and that no unauthorized person can access sensitive data.
3) Improving Accessibility
One of the standout benefits of pairing unattended devices with remote management is enhanced accessibility. With this setup, your remote IT team can connect to and control these devices, let’s say, unattended remote desktops, anytime, from anywhere. This flexibility means you’re not bound by location or time constraints, making it easier to keep everything running smoothly.
Types of Businesses That Benefit From Unattended Devices and Remote Management
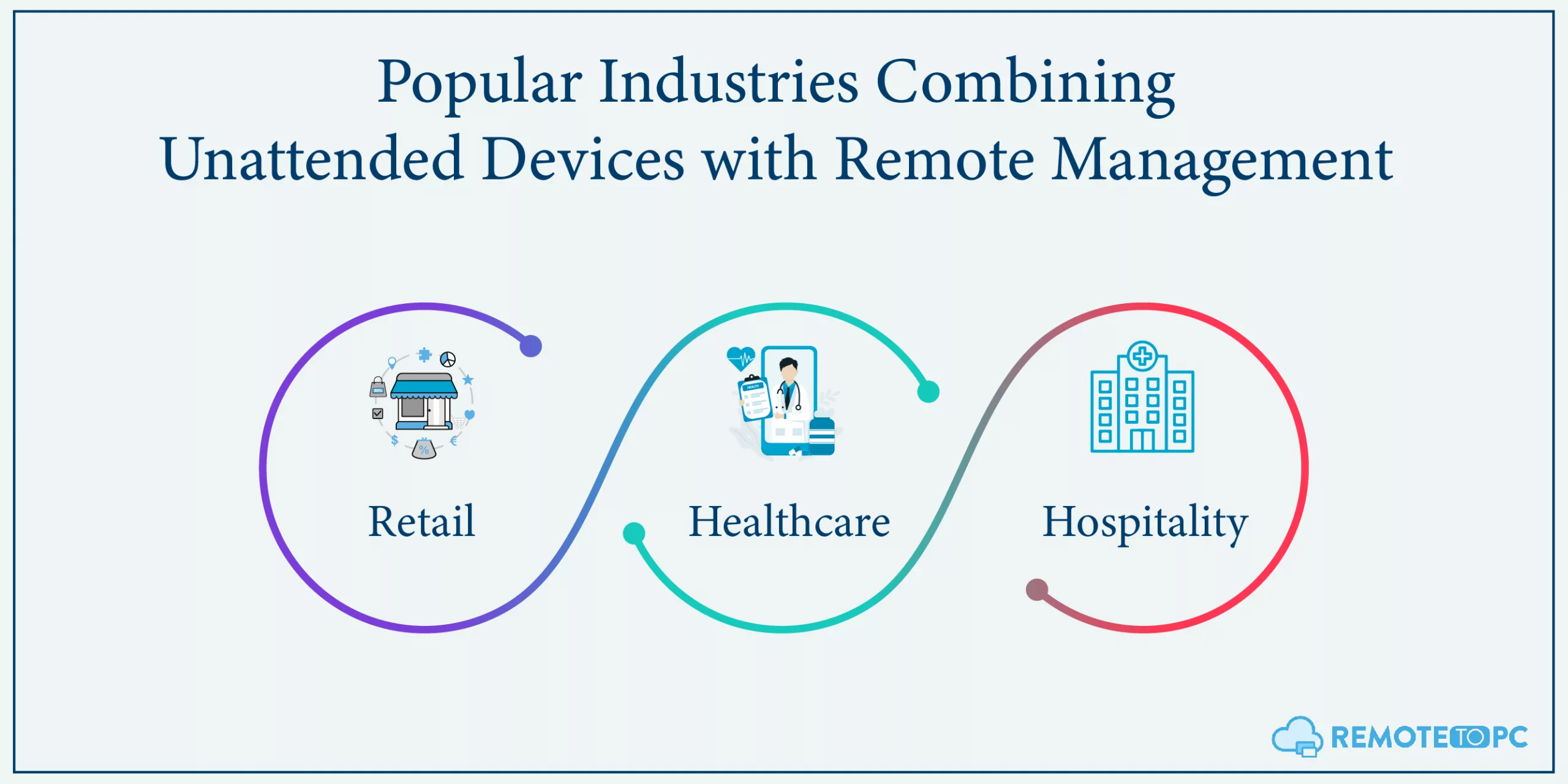
One of the best things about unattended gadgets and remote management is that it’s not restricted to a single industry. Below, we break down some industries where this integration can be particularly transformative.
Retail
Retail businesses often use self-checkout machines, price scanners, and even smart shelves. With remote management, they can get quick updates, especially email alerts, and troubleshoot potential IT issues. This helps them ensure a smooth customer experience.
Healthcare
In the healthcare sector, unattended devices often include information kiosks or telemedicine stations. These devices offer a convenient way for patients to access medical information or connect with healthcare providers. Remote management ensures that these stations are operational and secure- in compliance with the set regulations (HIPAA, GDPR, and PCI). It further allows them for timely updates and the safe handling of sensitive patient data.
Hospitality
In the hospitality industry, digital kiosks for self-service check-ins and automated food ordering have become increasingly popular. Remote management of these unattended devices is a game-changer. It allows for instant updates and ensures the machines are always functioning well, which leads to a smoother guest experience. Essentially, it gives hotels and restaurants a way to meet customer expectations efficiently and without hassle.
Setting Up Unattended Devices for Remote Management
When it comes to maximizing the benefits of unattended devices, implementing the right remote access technology for management is crucial. Here’s how to set everything up effectively:
1) Choosing the Right Devices
The first step is picking the right gadgets for your business. Think about what tasks these devices will do. Will they scan prices, give information, or do something else? Make sure to choose devices that are durable and reliable, like a remote desktop for easy remote login. After all, these gadgets will often work on their own, so they need to be up for the job.
2) Necessary Infrastructure
Next up is setting the stage, or in technical terms, the ‘infrastructure.’ This involves choosing how you’ll control the devices. One good option is remote desktop software like RemoteToPC, which lets you manage all your devices from one place. It will also assist the remote company operations with features like multi-to-multi pop-out screens, remote printing, and drag-and-drop file copy. It’s like having a remote control for all your gadgets.
3) Installation and Initial Configuration
Once you have your devices and control system, you need to set them up. One handy approach is to opt for secure remote working software with Zero-configuration installation. This feature makes the setup process a breeze, as the devices are designed to automatically establish a connection and configure themselves when turned on. In other words, no need to wrestle with complicated settings or technical jargon; just plug them in, and they’re good to go.
4) Connectivity Considerations
Finally, consider how these devices connect to the internet or other networks. Good connectivity is crucial for unattended devices’ safety and remote management. Make sure the devices can connect easily and stay connected. If they lose connection, you won’t be able to manage them from afar, and that could be a big problem.
Security Considerations
After setting up your device and software, the final step is to be vigilant about security in order to protect both hardware and sensitive data. Below are some key aspects to consider:
1) Physical Security
When you have devices that work on their own, it’s essential to think about their physical safety. Generally, it’s recommended to place them in a location where they’re hard to tamper with or steal. You can also use things like security cables or locked cabinets to help keep them safe.
2) Data Encryption and Firewalls
To keep your unattended devices secure, use data encryption and firewalls. Encryption scrambles data so only authorized users can read it. Firewalls act like a filter, allowing only safe data to pass through. For even stronger security, implement 2-factor authentication for web login and double-password protection as provided by RemoteToPC. These measures boost your device’s defenses, making unauthorized access much more challenging.
3) Authentication Protocols
When connecting to your devices from far away, you need a good way to prove you’re the right person for the job. This is called authentication. It is a quite simple yet significant way to ensure information safety. For this, you can use passwords, digital keys, or even fingerprint scans to ensure only authorized users are getting in.
Final Words
Unattended devices, paired with remote management, are a powerful duo that can transform your business across industries. As a matter of fact, it’s not just a passing trend but an impressive way to elevate your business.
So, leverage its power with RemoteToPC and get your free 14-day trial today!
Frequently Asked Questions (FAQs)
What Are Unattended Devices?
Unattended devices are computers, servers, or other hardware that are operational but not actively monitored by a person. These devices often include office computers, servers running in remote locations, and IoT devices.
Why is Remote Management Necessary for Unattended Devices?
Remote management allows businesses to monitor, update, and control devices without requiring physical presence. This is especially crucial for unattended devices, as they can become vulnerable to security risks like unauthorized access, malware, or hardware failure if not appropriately managed.
How Does RemoteToPC Work for Managing Unattended Devices?
Remote To PC provides a secure and user-friendly platform to manage unattended devices. Once the Remote TO PC software is installed on target devices, it enables you to carry out tasks like remote monitoring, file transfer, and even making necessary updates.
What Should I Look For in a Remote Management Solution?
When choosing a remote management solution, consider factors like ease of use, scalability, compatibility with your existing infrastructure, security features, and cost. Make sure it supports the kinds of devices you use and has the management features you require.
Is Remote To PC Secure for Business Use?
Absolutely. Remote To PC uses advanced encryption methods and multi-factor authentication to ensure the security of remote connections.